Why is an Incident Response Plan Important?
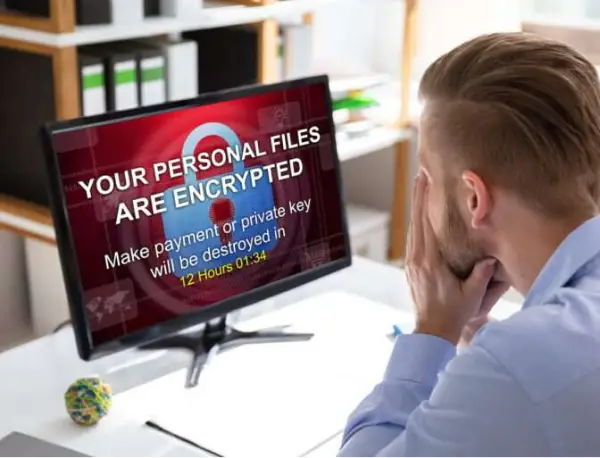
Understanding the Incident Response phases is very important. Having an incident response plan will help everyone involved perform correctly and within the law during an event Depending on the incident and the severity, you could be breaking the law if remediating. Did you know that if you received a Ransomware notice on your machine and shut it down, you may have just destroyed evidence? Depending on the severity of the attack and if there were exfiltration of data, there may be consequences.
IT Consultants should be very aware of this fact and even more so with Ransomware. If the IT consultant’s Client calls the IT Consultant to restore the firm’s information as fast as possible, your client’s insurance company may sue the IT Consultant for destroying evidence. Depending on the severity of the exfiltration, the IT consultant’s next problem is the state penalties. Therefore, it is so important to have these discussions.

Who is responsible for having an Incident Response Plan?
Any firm that has sensitive information should have an Incident Response Plan. If you use an IT consultant for your IT Services, the IT consultant should have an Incident Response Plan for you, the client, and themselves.
Phases of an Incident Response Plan
- Preparation
- Identification
- Containment
- Eradication
- Lessons Learned

It's Not "If" - It's "When!"
Preparing for Ransomware
The most feared cyber incident to a Law Firm is Ransomware. Most experts agree it is not if a Ransomware attack will happen, but when it will happen. Imagine your entire set of litigation documents (Document Review Platform) being encrypted and not being able to get to them for weeks. Will you be ready?
A Ransomware assessment will help you make the decisions you need to make during a Ransomware incident. Time is your enemy when it comes to a Ransomware attack. Having the answers to the basic questions will help you when you need the answers quickly.
When performing a Ransomware Assessment before an incident you will most likely not have to say; “How did we miss that?” Following a Framework like NIST fills in the gaps. Let’s stop the simple things from slipping through the cracks.
Ransomware Prevention
When you’re attacked, acting fast becomes a priority. Below are a few examples of what we can help with.
Client Audits


